- Identity governance could not scale up with business growth.
- Multiple on-premises IGA systems meant frequent expensive upgrades and third-party dependencies.
- Skill shortage made it difficult to manage IGA for 100+ apps.
How a Leading Middle Eastern Pharma Firm Modernized Its Identity Management with Microsoft Cloud-based IAM, Reducing Costs by 50%

Summary
The client, a prominent pharmaceutical company in the Middle East, successfully transitioned from an outdated on-premise Identity Governance & Administration (IGA) system to a cutting-edge cloud-based solution, achieving over 80% reduction in implementation cost and a 50% in maintenance costs. The implementation of Microsoft Cloud-based Identity and Access Management (IAM), utilizing Microsoft Entra Identity Governance, has not only enhanced security features but also integrated artificial intelligence, and streamlined operations across the client’s global network. This strategic upgrade has bolstered their security infrastructure, enabling more efficient and secure management of sensitive health data.
 Challenge
Challenge
 Solution
Solution
- Consulting, design, and implementation of a centralized cloud IAM
- Optimization of the existing MS cloud licenses to enhance compliance.
- Centralized identity management using Entra ID to reduce third-party reliance.
 Impact
Impact
- Automated workflows and centralized identity management reduced business disruptions and streamlined operations.
- Eliminating the need for investment in hardware saved Capex budgets and moved costs to Opex.
- AI-driven anomaly detection ensures better identity governance.
- Guaranteed compliance with HIPAA, PCI DSS, GDPR, and ISO 27001.

Overview
The customer is a leading pharmaceutical firm in the Middle East, known for its expansive operations and commitment to top-notch security in handling sensitive health data. Faced with increasing maintenance costs and system inefficiencies, the customer sought a modernized approach to identity management.
Specific Challenges
Cumbersome and inefficient legacy systems impacted operations and increased costs:
- High Maintenance Costs: Frequent need for hardware upgrades and compatibility fixes escalated costs.
- Complex and Error-Prone Systems: Integration issues and malfunctioning interfaces hindered the effective operation.
- Dependence on Vendor Support: Reliance on product vendors for integration support risked business continuity.
- Global Server Management: Over forty mission-critical servers worldwide lacked centralized monitoring, complicating oversight.
The Solution
As Paramount's Identity experts worked with the customer to implement Microsoft's Entra Identity Governance solution. Its key components included:
- Strategic Compliance Alignment: Tailored to meet rigorous standards such as HIPAA, PCIDSS, GDPR, and ISO27001, ensuring global compliance.
- Scalable Cloud Infrastructure: Implemented a flexible cloud infrastructure to manage extensive data securely and efficiently.
- Enhanced Identity Security: Provided robust identity management and access control within a single management pane, improving security measures.
- Operational Efficiency and Cost Reduction: Transitioned from capital to operational expenses, reducing maintenance with scalable infrastructure.
- Advanced Authentication and Customization: Moved user endpoints to cloud-based identity management, boosting security with modern authentication, custom access, and AI reviews.

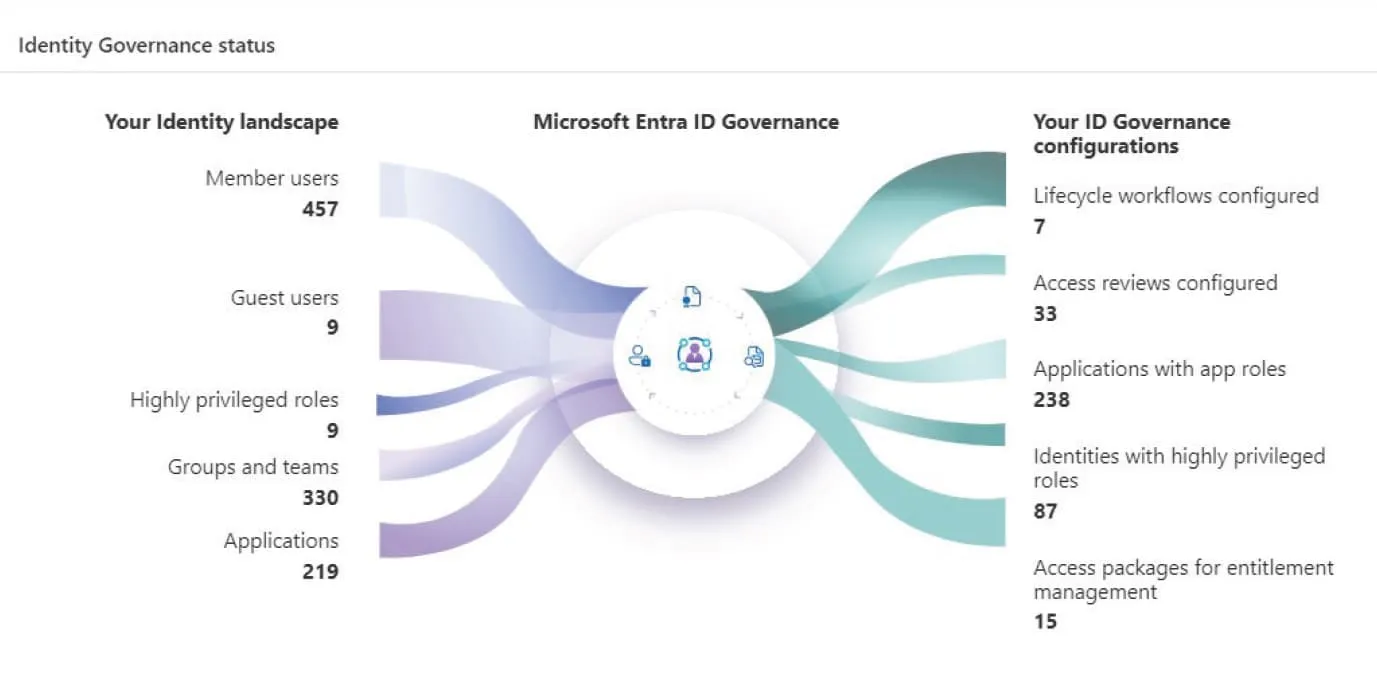
Microsoft Entra Identity Governance optimizes IAM operations:
Lifecycle Management
Automates employee lifecycle processes.
Entitlement Management
Simplifies automated access requests and assignments.
Access Reviews
Verifies necessary access for all users for compliance and security.
Privileged Identity Management
Controls and monitors privileged roles.
Terms of Use Enforcement
Enforcing compliance and security in resource access.
Impact
-
Effective User Lifecycle Management
Streamlined governance through a Single View Panel, enhancing visibility and efficiency with fewer resources. -
Enhanced Security and Compliance
Improved control and compliance via Microsoft Cloud-based IAM and Microsoft Entra Identity Governance. -
Significant Cost Reductions
Reduced implementation costs by over 80% (a reduction by 2 million Saudi riyals) and ongoing operational costs by 50%. -
Increased Efficiency in Access Management
Automated processes cut access provisioning and deprovisioning time significantly, boosting productivity. -
Seamless Integration and Operation
Supports seamless integration of cloud and on-premises applications, enhancing operational efficiency.

The Components of Microsoft Entra Identity Governance
Why choose Paramount Assure as your Identity and Access Management (IAM) solution partner for cutting-edge security and efficiency?
Paramount Assure’s Identity and Access Management (IAM) capabilities provide robust security and efficient management for enterprise systems. Their IAM solution offers advanced features like multi-factor authentication, single sign-on, and user access reviews, ensuring secure and streamlined access control. With its scalable architecture, it supports a range of industries, enhancing compliance and reducing security risks. Paramount Assure’s IAM tools are designed for ease of use, offering comprehensive reporting and policy enforcement options.

Microsoft Cloud-based Identity and Access Management (IAM) system
The Microsoft Cloud-based Identity and Access Management (IAM) system offers robust security features, streamlined access controls, and scalable management solutions across both cloud and on-premises environments, ensuring that users have secure and appropriate access to resources.

Microsoft Entra Identity Governance
Microsoft Entra Identity Governance provides comprehensive tools for managing and securing identities across your organization. It enhances security with automated lifecycle management, access reviews, and privileged identity management while enforcing compliance through detailed audit trails and adaptable entitlement policies, aligning with a Zero Trust security model.

