When addressing threats, every second is crucial. Even a slight delay can sabotage your organization’s integrity. With the evolving threat landscape, it can get challenging to respond in time.
This is where Microsoft Security Copilot is changing the game. Based on advanced AI algorithms, Microsoft CoPilot for Security has made fighting threats and protecting your organization simpler, faster, and more efficient than ever. The tool automates key security tasks, improves your threat intelligence, and simplifies your endpoint management to keep you a step ahead, at all times.
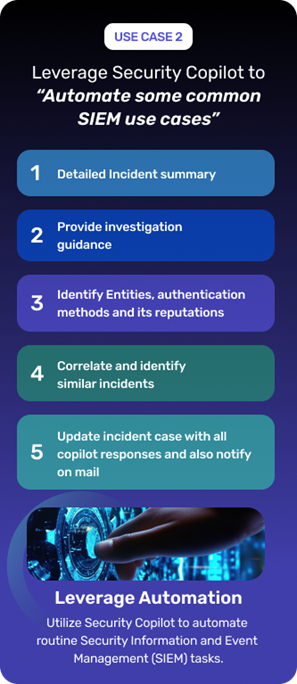
Centralize security alerts and responses enhancing your incident response efficiency. Proactively identify and mitigate threats, ensuring swift and effective security incident handling.
Provides a seamless platform for incident response: Coordinate and manage all security alerts, actions, and responses from a centralized control center.
Enables security teams to identify and mitigate security threats efficiently: Establish a proactive warning system that alerts you to potential threats before they become major problems.
Enhances your ability to respond to security incidents: Accelerate your response process and ensure that all security incidents are handled swiftly and effectively.
Reduce time and efforts by automating compliance reporting and audit log collection. Streamline compliance maintenance, error identification, and oversight prevention efficiently.
Automates Compliance Reporting and Collection of Audit Logs: Automate document and audit log collection to demonstrate compliance on time during audits.
Streamlines Maintaining Compliance: Track compliance requirements, identify errors, and prevent oversights without much manual intervention.
Reduces Time and Effort for Compliance Activities: Free up your resources to focus on other security matters and governance activities.
Boost cybersecurity knowledge across your team with AI-driven training and querying. Enhance security operations by empowering more personnel, regardless of technical expertise.
Assists in upskilling the knowledge of cybersecurity professionals: Amplify the security skill set across your workforce with AI-driven training and querying.
Reduces dependency on specialized skill sets: Strengthen your security infrastructure and resilience with advanced cyber security knowledge at your fingertips.
Enhances the efficiency of security operations: Improve your overall security posture by empowering more personnel to handle your security tasks, even without requiring technical know-how.
Empower non-technical staff to tackle complex security issues effortlessly. Simplify threat investigations with easy querying and gain comprehensive insights to handle threats effectively.
Empowers non-technical personnel to solve complex issues: Enable all your employees and personnel to solve complex security issues.
Reduces complexity in querying and investigation: Simplify threat investigation and collating necessary information with easy querying.
Provides comprehensive insights and actionable intelligence: Gain actionable recommendations on dealing with and preventing threats and vulnerabilities.
Cut detection time with Microsoft Defender Threat Intelligence. Combine external and internal data for a clear view of threats, automating analysis and enabling faster, efficient responses.
Integrates with Microsoft Defender Threat Intelligence: Gain a comprehensive view of the threat landscape and spot potential vulnerabilities before they are exploited.
Correlates external threat data with organizational data: Tap into the global intelligence network and establish a proactive response system with real-time insights on cyber threats.
Reduces the time required for threat analysis and incident response: Automate threat detection and enable faster responses, saving hours on manual analysis.
Elevate your cloud security with streamlined operations and enhanced threat insights. Safeguard your data and apps while automating security tasks for simplified management.
Enhances the security of cloud environments: Protect your data and applications in the cloud and safeguard your valuable assets.
Provides insights into security threats and vulnerabilities within cloud infrastructure: Set up a system that constantly scans your cloud environment for any signs of trouble.
Streamlines security operations in cloud environments: Automate security tasks and gain clear insights to simplify cloud security management.
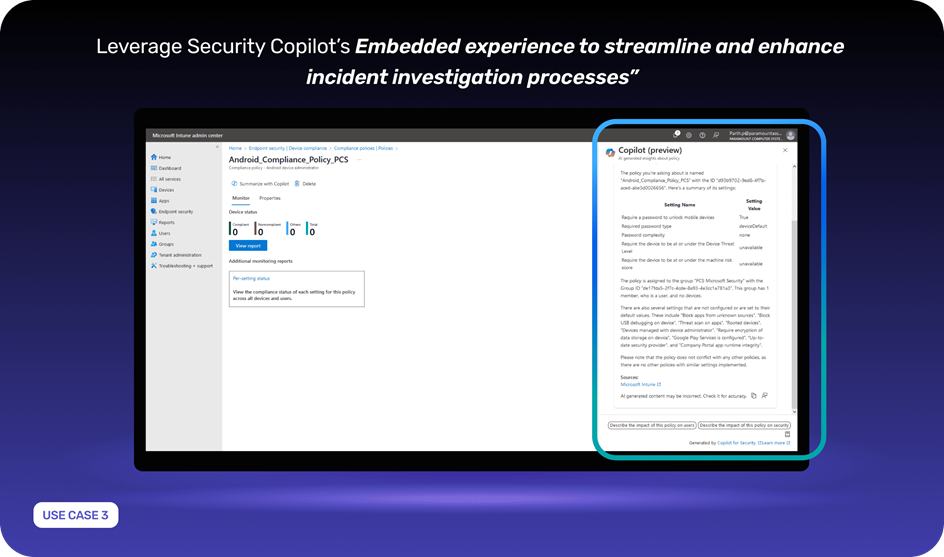
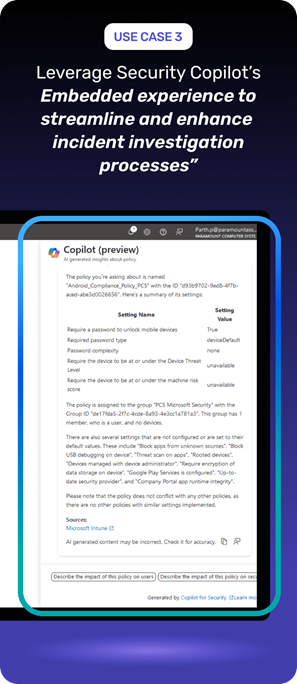
Centralize endpoint monitoring for streamlined security and threat detection. Automate security responses and compliance checks, enhancing endpoint security effortlessly across devices.
Streamlines the security and management of endpoints: Establish centralized monitoring capabilities to streamline endpoint threat detection and security management.
Enhances endpoint security monitoring and response: Automate endpoint security monitoring and gain actionable insights to improve security strategies.
Identifies compliance status for all devices: Gain clear visibility into the compliance status of all devices, ensuring adherence to security policies and regulations.